Defguard vs NetBird: Enterprise VPN vs WireGuard Mesh (2026)
March 13, 2026 • Robert Olejnik
9 min to read
Netbird is primarily a cloud service that provides VPN functionality focusing on the WireGuard® mesh networking (one network) paradigm for ease of use. While it can be deployed on-premises to some extent, it requires all components (both the control and data planes) to be publicly exposed. This creates a broader attack surface and represents a single point of failure.
In contrast, Defguard is an on-premises-first Enterprise VPN solution, built for secure remote access using a secure-by-design architecture and service segmentation. Its control plane, which integrates with external SSO and IdP solutions, is never exposed to the public internet. This ensures that all public-facing components remain stateless and secure, while also delivering the centralized network management that Enterprise customers expect.
Whether using the cloud or the on-premises version, Netbird requires all components to be launched within a single network (e.g., on a single machine or a single Docker network) and then collectively exposed to the public internet.
This approach shares the same inherent weakness as the SSL VPN architecture now being phased out by most enterprise vendors (see Fortinet’s move to IPsec). Most attacks do not target the VPN protocol itself, but rather the management endpoints of these solutions. In the case of SSL VPNs, there are two primary vulnerabilities:
Despite using the superior WireGuard® protocol, Netbird follows this same risky security model by exposing both the control and data planes to the public internet. This approach provides more the ease of architecture, deployment and feature development but is not expected in Enterprise environments.
In contrast, Defguard was designed with security as the most important factor delivering the secure-by-design (SBD) approach (detailed information about SBD) where the most differentiating factor is segmentation of systems and components.
The communication between the components is designed to prevent lateral movement from public (proxy, gateway) to private (core) network segments. This can be achieved in several ways on the network level, e.g. through separate VLANs or multiple firewalls.
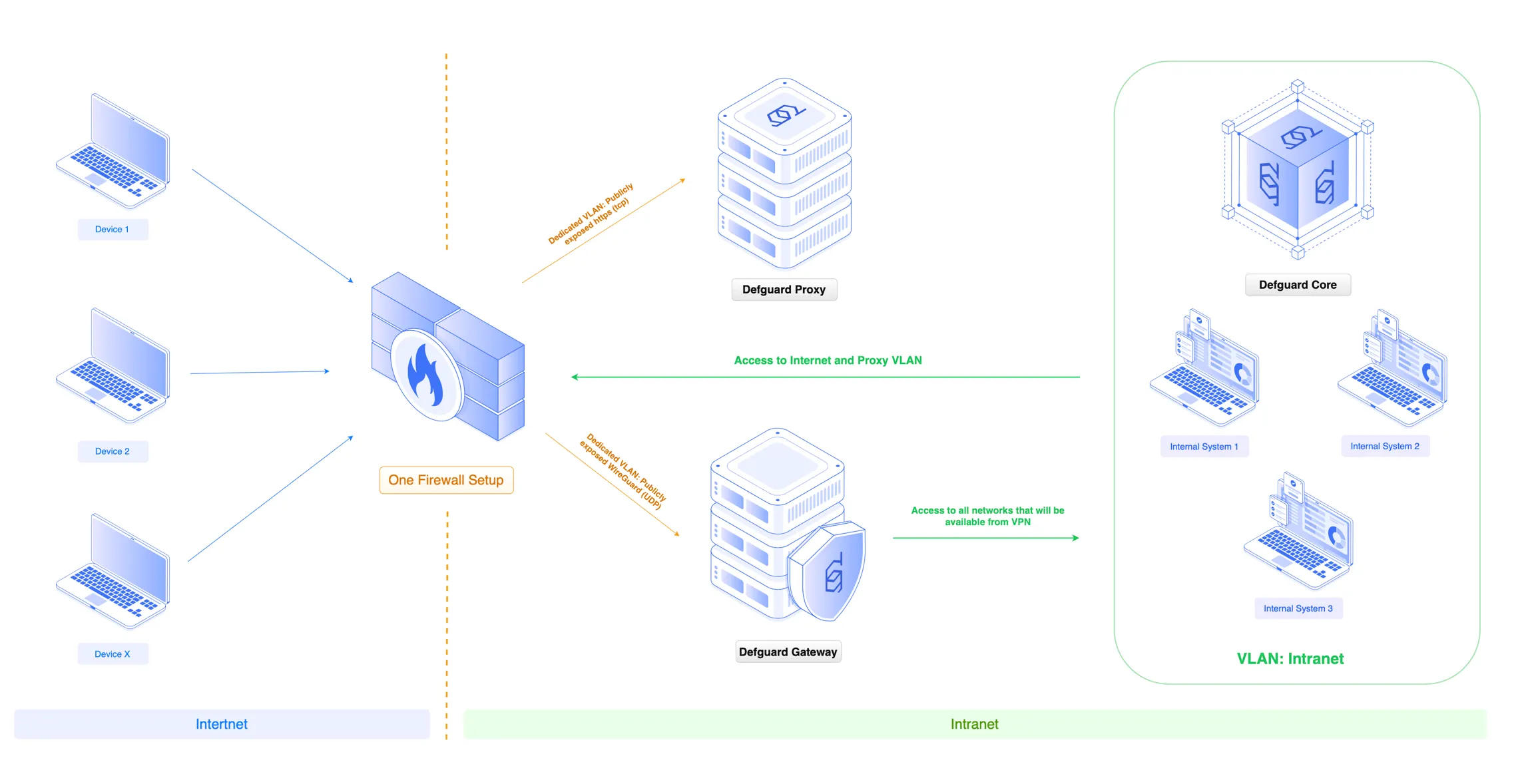
The segmented approach significantly reduces attack surface and makes the system more resilient.
While Netbird only supports MFA through external SSO providers, Defguard goes further. In addition to supporting the same external SSO providers, Defguard enables various other MFA methods, including:
Furthermore, while Netbird’s authentication only handles peer configuration, Defguard’s MFA provides multiple security layers, including the exchange of additional security keys.
Netbird is implemented in Go, whereas Defguard is written in Rust—a memory-safe language favored for security and recommended by nearly all top-tier security organizations worldwide:
Mesh networking (used by Netbird) provides flexibility and ease of use, but is often unsuitable for Enterprise environments for several reasons:
Defguard adheres to enterprise standards by providing centralized network management (which directly resolves the issues listed above), while also delivering several key network advantages, such as:
While Netbird supports running multiple Relay/STUN servers via manual configuration—allowing clients to randomly select a relay and automatically fail over if one goes down—running the core control and data plane servers concurrently for High Availability (HA) is not officially supported out-of-the-box for self-hosters. Instead, the standard approach is to rely on orchestration tools like Kubernetes or Docker Swarm to monitor container health and instantly spin up a replacement if a crash occurs.
Defguard (from version 2.0) provides Active-Active High Availability of Edge and Gateway components with easy UI management and automated adoption.
By taking advantage of a centralized networking model, Defguard delivers several advanced features unavailable in Netbird.
Defguard’s structure reflects a typical corporate environment through VPN Locations, allowing you to control access and connect to specific sites directly.
Unlike Netbird, which displays a flat ‘peer’ list that becomes nearly impossible to manage with thousands of users and devices, Defguard maintains a clear, hierarchical User and Device structure. This enterprise-ready approach includes:
While we’ve discussed the limitations of mesh networking for large enterprises, it’s only fair to acknowledge why it became so popular in the first place. For smaller, agile teams without dedicated IT departments, the mesh paradigm (like Netbird or Tailscale) offers some very compelling features:
Netbird’s Posture Checks are a core component of its Zero Trust Network Access (ZTNA) framework, designed to verify a device’s security compliance before granting network access. By evaluating real-time telemetry such as operating system versions, geographic location, and the presence of specific security processes or certificates Posture Checks ensure that only healthy, authorized devices can connect to sensitive resources.
In Defguard Device Posture Checks are planned in version 2.1 (early Q2 2026).
Netbird simplifies network navigation through its Magic DNS feature, which automates peer-to-peer hostname resolution and eliminates the need for manual host file management. This system is further enhanced by support for split-DNS routing, allowing administrators to precisely direct internal domain queries to specific private servers while keeping other traffic on public paths. Beyond internal naming, Netbird also offers the flexibility to configure Custom DNS resolvers, enabling teams to integrate external or existing corporate DNS servers to ensure consistent and secure name resolution across the entire distributed mesh network.
In Defguard Split DNS and Magic DNS is planned in version 2.3.
NetBird streamlines the delivery of internal resources through its Service Exposure functionality, leveraging an integrated reverse proxy to securely publish private applications. This feature allows administrators to map internal web services to specific hostnames accessible only within the encrypted mesh, effectively eliminating the need to open vulnerable ports to the public internet. NetBird enables seamless access to internal tools and dashboards with ease which is a great feature for development teams.
Netbird provides MDM Integration, supporting industry-standard platforms like Kandji, Jamf, and Microsoft Intune. This feature automates the synchronization of device metadata, allowing administrators to maintain a real-time, unified inventory of all endpoints within the mesh network.
Netbird integrates with leading EDR platforms (such as CrowdStrike and SentinelOne) to leverage real-time threat telemetry. By continuously verifying the status of the local EDR agent, Netbird can automatically restrict or revoke network access for any endpoint that becomes infected or compromised, providing an essential layer of automated threat containment across the distributed mesh.
Choose Defguard when you need enterprise-grade security: isolated control plane, centralized traffic inspection, compliance-ready logging (SOC2, ISO27001, NIS2), and hierarchical user/device structure. Ideal when reducing attack surface and meeting audit requirements are non-negotiable.
Choose NetBird when you’re a small team prioritizing zero infrastructure, direct peer-to-peer speed, and plug-and-play connectivity—and when Device Posture, Magic DNS, Service Exposure, MDM, or EDR integration are essential today.
Both use WireGuard®. The difference is architecture, security model, and target environment. For enterprises, Defguard’s secure-by-design approach and control plane isolation deliver the resilience and visibility that compliance and security teams expect.
| Feature | Defguard | NetBird |
|---|---|---|
| Control plane exposure | Never exposed; isolated on internal network | All components publicly exposed |
| Implementation language | Rust (memory-safe) | Go |
| Network model | Centralized gateway; traffic inspection possible | Mesh; peer-to-peer; no central inspection |
| Native MFA (TOTP, Email, Biometrics) | Yes—multiple methods built-in | MFA only via external SSO |
| Multiple VPN networks (IPv4 & IPv6) | Yes | Single flat IPv4 network |
| Static IP per user/device | Yes (v2.0+) | No |
| Active-Active High Availability | Yes (v2.0+), UI management | Relay/STUN failover; core HA not officially supported |
| Device Posture Checks | Planned v2.1 (early Q2 2026) | Yes—OS, location, EDR status |
| Magic DNS / Split DNS | Planned v2.3 | Yes |
| Integrated application proxying | Forward Auth for reverse proxies | Yes—Service Exposure feature |
| MDM integration (Kandji, Jamf, Intune) | Zero-touch enrollment | Yes—device metadata sync |
| EDR integration (CrowdStrike, SentinelOne) | — | Yes—auto restrict/revoke on threat |