MFA for WireGuard®: How to Meet NIS2 Directive Requirements
October 7, 2025 • Piotr Borkowicz
6 min to read
Organizations seeking compliance with the NIS2 Directive must implement Multi-Factor Authentication (MFA) as a crucial layer of defense for remote access.
In this article, we’ll explore the core challenge this presents for teams using VPNs with the WireGuard® protocol, and how Defguard provides the definitive solution by enabling true, connection-level MFA. For a broader vendor comparison, see our OpenVPN Access Server alternative guide.
The NIS2 Directive (Network and Information Security Directive) builds upon its predecessor with more stringent requirements aimed at bolstering cybersecurity resilience. For remote access, the directive is clear:
It mandates that organizations implement stronger security measures to protect networks, systems, and data. A key component of this is the focus on MFA for all access points, including VPNs.
This presents a significant challenge. The WireGuard® protocol has become the foundation for modern, high-performance VPNs due to its speed and simplicity.
However, the WireGuard® protocol itself does not include any native concept or mechanism for Multi-Factor Authentication. This architectural reality means that a standard VPN built with WireGuard® is not inherently NIS2 compliant for MFA.
According to the 2025 Verizon DBIR, around 60% of all breaches involved compromised credentials. Relying solely on a WireGuard® key pair—a single factor—leaves a critical security gap that fails to meet the layered defense principle required by NIS2.
Defguard is designed specifically to solve this problem by adding a robust, true MFA layer directly on top of the WireGuard® protocol.
It ensures that even if a user’s private key is compromised, unauthorized access is blocked by requiring a second factor before the VPN connection is established.
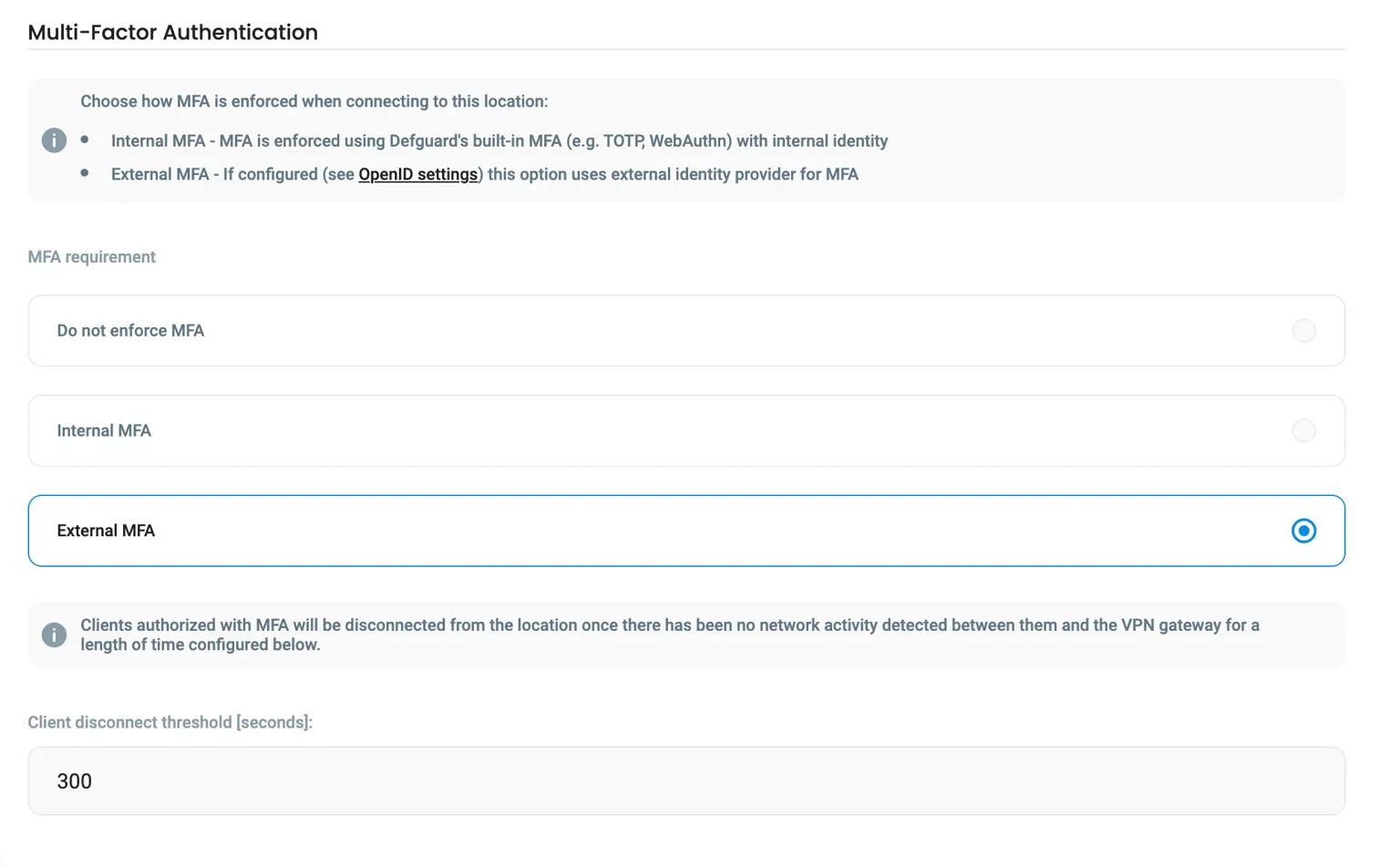
Defguard integrates with modern MFA mechanisms directly at the VPN connection level. Supported methods for the VPN connection include:
This makes managing and deploying MFA for your VPN straightforward, enabling organizations to meet regulatory requirements while benefiting from WireGuard®’s performance advantages.
The term “VPN MFA” is often used broadly, but its implementation varies significantly. Many solutions apply MFA only at the application layer—for instance, protecting a web panel or the initial client setup.
While this offers some security, it leaves a critical gap: it does not secure the VPN connection itself.
Defguard’s approach is fundamentally different and unique: it is the only solution that enforces true Multi-Factor Authentication directly at the WireGuard® protocol level, before any connection is established.
This architectural distinction means that no traffic can enter your network without first passing an MFA check, providing a superior security posture essential for NIS2 compliance. This ensures protection even if WireGuard® private keys are compromised.
Learn more about our approach to true, connection-level VPN MFA.
| MFA Method | Best For (Use Case) | How it Works |
|---|---|---|
| Biometrics | Fast, secure access from trusted personal devices (laptops, phones). | Uses fingerprint or face scan on the user’s device to approve connection. |
| One-Time Passwords (OTP) | Universal compatibility and offline access scenarios. | User enters a 6-digit code from an authenticator app (e.g., Google Auth). |
| External IdP/SSO | Integrating with existing corporate identity systems. | Leverages the MFA policies already set in your company’s Google, Microsoft, or Okta. |
The WireGuard® protocol has quickly become the preferred foundation for modern VPNs, offering distinct advantages that make it an excellent choice for securing network access. Its design principles deliver superior performance and reliability.
While Defguard excels at integrating MFA with VPNs using the WireGuard® protocol, its functionality extends far beyond that.
It provides a comprehensive security management toolkit for various aspects of compliance and administration. After solving the core MFA problem, you can leverage features like:
Defguard helps organizations manage digital identities across their network infrastructure. This is crucial for compliance with not only NIS2 but other regulations like GDPR.
SSO functionality is another powerful feature. It simplifies the user experience by allowing employees to use one set of credentials to access multiple applications, reducing password fatigue.
By integrating with external OpenID providers or using the built-in IdP based on the OpenID Connect standard, Defguard creates a secure and user-friendly authentication experience.
Another vital feature is the ability to manage hardware keys like YubiKeys.
While Defguard offers robust YubiKey management for functions like SSH and GPG keys, it’s important to note that hardware keys are not currently used as a second factor for the VPN connection flow itself.
Implementing MFA requires careful planning to ensure it doesn’t become cumbersome.
The NIS2 Directive elevates Multi-Factor Authentication from a best practice to a legal necessity for securing VPN access. The path to compliance for teams using the WireGuard® protocol is direct:
Organizations must implement stronger security measures to protect networks, systems, and data, with a key component being the focus on MFA.
Solutions like Defguard make this straightforward by integrating true, connection-level MFA directly into your VPN. This provides a comprehensive, regulatory-compliant strategy to ensure your critical systems remain protected.
No. The base WireGuard® protocol does not include a native MFA mechanism, which is a key technical requirement for access control under the NIS2 Directive.
Defguard supports true, connection-level MFA using Biometrics, Time-based One-Time Passwords (TOTP), and integration with external SSO providers like Google, Microsoft, Okta, and JumpCloud. For a full list of supported providers, see our documentation.
Defguard is the only open-source platform that enforces MFA at the WireGuard® protocol level, not just at an application login. This provides a fundamentally higher level of security required for compliance.
Piotr Borkowicz
Technical Writer, Defguard
defguard.net